The Power of Elegant Simplicity #1: Shamir's Secret Sharing - The Polynomial That Guards Your Secrets
Part of the “The Power of Elegant Simplicity” series - algorithms that hide power in plain sight
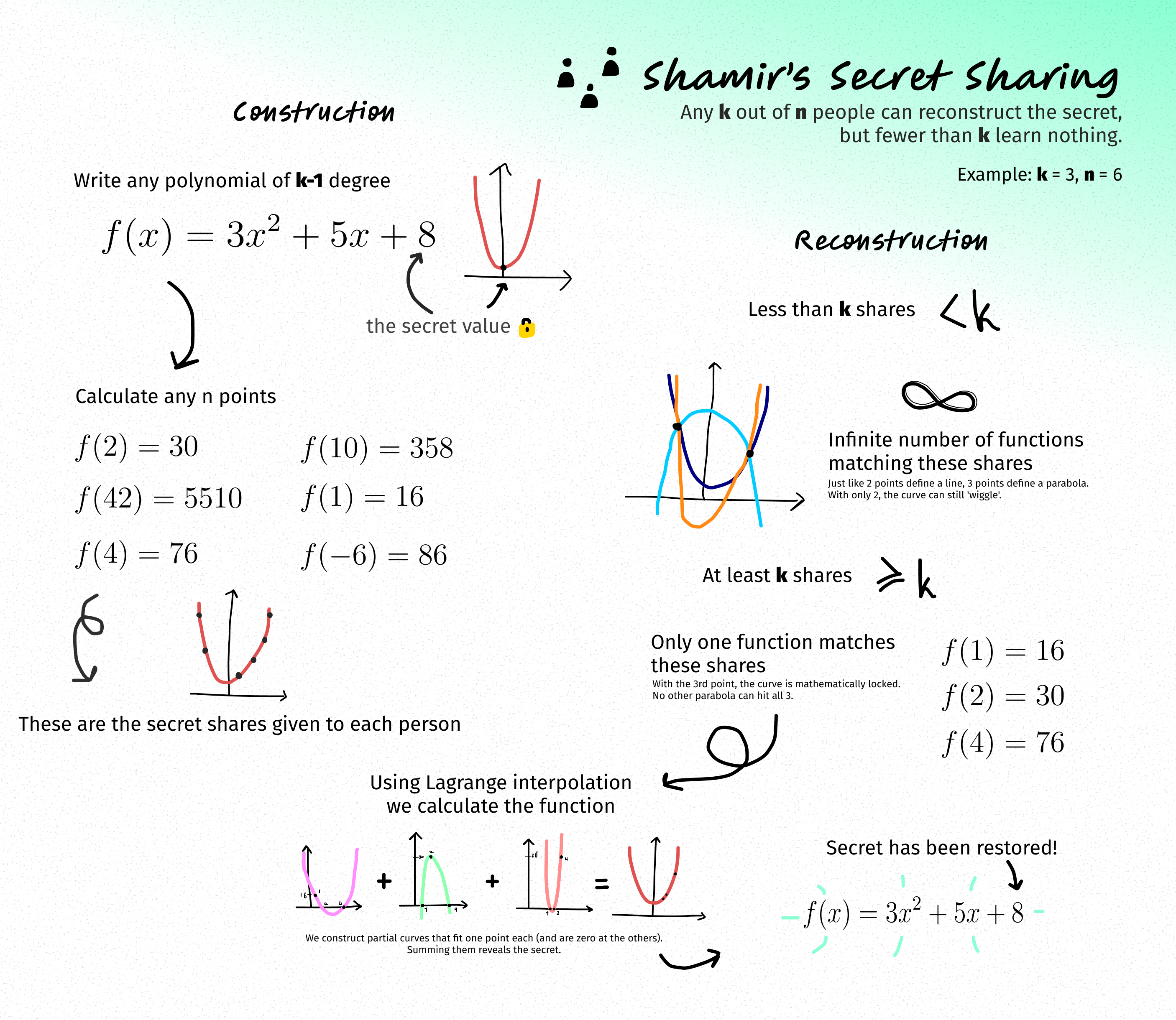
You know what’s wild? One of the most elegant cryptographic algorithms ever invented uses nothing more than high school algebra. No complex number theory, no quantum mechanics, just polynomials. The kind you probably learned to hate in 9th grade.
Welcome to Shamir’s Secret Sharing, where a simple quadratic equation becomes the foundation for securing nuclear launch codes, cryptocurrency wallets, and anything else you really, really don’t want falling into the wrong hands.
The Problem: Trust No One (But Trust Everyone Together)
Imagine you’re a startup founder with the keys to your company’s crypto wallet. If you keep them yourself, you’re one bike accident away from locking everyone out forever. If you give copies to your co-founders, any one of them could clean out the account and disappear to Bali.
What you need is a way to split a secret so that:
- No single person can reconstruct it alone
- But any group of, say, 3 out of 5 people can work together to recover it
- People who don’t have enough shares learn absolutely nothing (not “almost nothing” - literally nothing)
This is exactly what Adi Shamir figured out in 1979. And the solution is beautifully simple.
The Trick: It’s Just a Polynomial
Here’s the entire algorithm in one sentence: encode your secret as a point on a polynomial, give each person a different point, and use the magic of polynomial interpolation to reconstruct it.
That’s it. No, really.
Let’s break it down with an example where we want 3 people to be able to reconstruct the secret, out of 6 total people (k=3, n=6).
Step 1: Encode Your Secret
Let’s say your secret is the number 8 (maybe it’s a password hash, or a piece of an encryption key).
Create a polynomial of degree k-1 (so degree 2 in our case) where the constant term is your secret:
1 | f(x) = 3x² + 5x + 8 |
The coefficients 3 and 5? Completely random. Throw dice. Mash your keyboard. Doesn’t matter. But that 8? That’s your secret, hiding in plain sight at f(0).
Step 2: Generate the Shares
Now just evaluate your polynomial at different points:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 | def create_shares(secret, k, n): """ Split a secret into n shares where k shares are needed to reconstruct. Args: secret: The secret value to share k: Minimum number of shares needed to reconstruct n: Total number of shares to create """ import random # Create a polynomial of degree k-1 with secret as constant term coefficients = [secret] + [random.randint(1, 100) for _ in range(k-1)] def polynomial(x): return sum(coef * (x ** i) for i, coef in enumerate(coefficients)) # Generate n shares by evaluating polynomial at different points shares = [(i, polynomial(i)) for i in range(1, n + 1)] return shares # Example usage secret = 8 shares = create_shares(secret, k=3, n=6) # With coefficients [8, 5, 3] this gives us: # [(1, 16), (2, 30), (3, 50), (4, 76), (5, 108), (6, 146)] |
Give person #1 the point (1, 16), person #2 gets (2, 30), and so on. These are your shares.
Step 3: The Magic of Reconstruction
Here’s where it gets cool. With fewer than 3 shares, there are infinitely many polynomials that fit through those points. Just like two points define a line but could be part of any parabola, two shares from our 2nd-degree polynomial could match an infinite number of possible secrets.
But the moment you have 3 shares, boom - there’s exactly one polynomial of degree 2 that fits through all three points. Mathematics locks it in.
We use Lagrange interpolation to reconstruct the polynomial:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 | def lagrange_interpolation(shares): """ Reconstruct the secret using Lagrange interpolation. Args: shares: List of (x, y) tuples representing shares Returns: The secret (value at x=0) """ def basis_polynomial(i, x): """Calculate the i-th Lagrange basis polynomial at x""" xi, yi = shares[i] result = yi for j, (xj, yj) in enumerate(shares): if i != j: result *= (x - xj) / (xi - xj) return result # Evaluate the interpolated polynomial at x=0 to get the secret secret = sum(basis_polynomial(i, 0) for i in range(len(shares))) return round(secret) # Reconstruct with any 3 shares secret_recovered = lagrange_interpolation([(1, 16), (2, 30), (4, 76)]) print(f"Secret: {secret_recovered}") # Output: Secret: 8 |
The polynomial gets reconstructed, and f(0) gives us back our secret.
Why This is Actually Mind-Blowing
Perfect Security: If you have k-1 shares, you have zero information about the secret. Not “very little” - literally zero. The secret could be any value with equal probability. This is information-theoretic security, the same kind that makes one-time pads unbreakable.
Flexibility: Want to go from 5 shares to 10? Just evaluate the same polynomial at new points — instant new shares. Want to update the secret entirely? Generate a new polynomial and distribute fresh shares. One caveat: if you need to change the threshold (say, from “3 of 5” to “4 of 7”), that means a new polynomial of a different degree, so you’d need to redistribute all shares.
Simplicity: The entire algorithm fits in a tweet. Okay, maybe a long tweet. But still.
Real-World Applications
This isn’t just a clever party trick. Shamir’s Secret Sharing is used in:
- Cryptocurrency wallets: Splitting recovery seeds across multiple devices or people
- Certificate authorities: Requiring multiple executives to sign off on root certificates
- Nuclear launch codes: Academic example because you definitely want more than one person to agree on this
- Distributed password managers: Like Hashicorp Vault’s unseal process
- Threshold signatures: Multiple parties cooperating to sign transactions
The Catch (There’s Always a Catch)
Like most cryptographic primitives, the devil is in the implementation details:
-
Random number generation matters: Those random coefficients need to come from a cryptographically secure random number generator (CSPRNG), like Python’s
secretsmodule. The standardrandommodule is a regular PRNG — predictable if someone knows the seed. (The code examples in this post userandomfor clarity, but don’t do that in production.) -
Share storage is critical: Each share is as sensitive as the original secret. If someone gets k shares, game over.
-
No integrity protection (mostly): Basic Shamir doesn’t have built-in authentication, but here’s a neat trick — if you collect more than the minimum k shares, you can catch liars. Just try reconstructing from different subsets of k shares. If everyone’s honest, every subset gives the same secret. If someone faked their share, the subsets containing it will produce a different result, exposing the liar. Fair warning: this gets expensive fast (the number of subsets grows combinatorially), so it’s more of a sanity check than a scalable defense. For real-world use, look into verifiable schemes like Feldman’s VSS or Pedersen’s VSS.
-
Computation in finite fields: For production use, you need to work in finite fields (modulo a large prime) to avoid floating-point precision issues and information leakage.
-
Other production concerns: A full deployment would also want share authentication (MACs or signatures on each share), replay protection, and possibly proactive secret sharing — periodically refreshing shares without changing the secret. These are beyond our scope here, but worth knowing about if you ever build this for real.
The Modular Twist: From Theory to Practice
That last point deserves its own section, because it’s both important and surprisingly simple.
Everything I explained above works algebraically over the real numbers — the polynomial math is correct, and you’ll get your secret back. But here’s the thing: over ℝ, the scheme doesn’t actually provide information-theoretic security. The range and magnitude of the share values can leak information about the secret. The “zero knowledge with k-1 shares” guarantee only holds in a finite field. So modular arithmetic isn’t just a practical fix for computers — it’s a security requirement. Let me explain.
Why Modular Arithmetic?
Problem 1: Floating-point chaos
When you reconstruct a polynomial using Lagrange interpolation with real numbers, you’re doing lots of divisions. These create fractions that computers represent as floating-point numbers. After a few operations, you might get 7.999999999998 instead of 8. Usually you can just round, but what if your secret is 7 or 8? At scale, these errors compound.
Problem 2: Information leakage
Here’s a subtler issue. If someone has k-1 shares and sees the intermediate calculations, the size of those numbers might reveal information about the secret. In real arithmetic, evaluating a degree-2 polynomial at x=100 gives much bigger results for some coefficients than others. An attacker could use this to narrow down possibilities.
The solution: Work modulo a prime
Instead of doing arithmetic over all real numbers, we do everything modulo a large prime number p. This means:
- All values stay in the range [0, p-1]
- No floating-point numbers at all - everything is integers
- Division becomes “multiplication by the modular inverse”
- Every value is equally likely, revealing nothing
How Simple Is The Change?
Remarkably simple. Take any operation from the basic algorithm and add % prime at the end:
1 2 3 4 5 | # Basic (problematic) result = (result * x + coef) # Modular (production-ready) result = (result * x + coef) % prime |
The only tricky part is division. In modular arithmetic, you can’t just divide - instead, you multiply by the modular inverse. If you want to compute a / b mod p, you calculate a * (b^(-1)) mod p, where b^(-1) is the number such that b * b^(-1) ≡ 1 (mod p).
Python 3.8+ makes this trivial:
1 2 | # Division in modular arithmetic result = (a * pow(b, -1, prime)) % prime |
That’s it. The entire conceptual framework - polynomials, shares, interpolation - stays exactly the same. You’re just doing the arithmetic in a different “universe” where numbers wrap around at prime.
Choosing Your Prime
The prime p needs to be larger than:
- Your secret value
- The number of shares you’ll create
A common choice is a Mersenne prime like 2³¹ - 1 or, for cryptographic applications, a 256-bit prime. The “Try It Yourself” example below uses modular arithmetic properly.
Try It Yourself
Here’s a complete, simple implementation you can play with:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 | import random def create_shares(secret, k, n, prime=None): """Create n shares of a secret with threshold k""" if prime is None: prime = 2**31 - 1 # Mersenne prime for simplicity # Random coefficients for polynomial coefficients = [secret] + [random.randint(0, prime - 1) for _ in range(k - 1)] def evaluate(x): """Evaluate polynomial at x using Horner's method""" result = 0 for coef in reversed(coefficients): result = (result * x + coef) % prime return result # Generate shares shares = [(i, evaluate(i)) for i in range(1, n + 1)] return shares, prime def reconstruct_secret(shares, prime): """Reconstruct secret from shares using Lagrange interpolation""" secret = 0 for i, (xi, yi) in enumerate(shares): numerator = denominator = 1 for j, (xj, _) in enumerate(shares): if i != j: numerator = (numerator * (0 - xj)) % prime denominator = (denominator * (xi - xj)) % prime # Modular inverse for division in finite field lagrange_coef = (numerator * pow(denominator, -1, prime)) % prime secret = (secret + yi * lagrange_coef) % prime return secret # Example secret = 12345 shares, prime = create_shares(secret, k=3, n=5, prime=104729) print(f"Original secret: {secret}") print(f"Shares: {shares[:3]}") # Show first 3 shares # Reconstruct with any 3 shares recovered = reconstruct_secret(shares[:3], prime) print(f"Recovered secret: {recovered}") |
The Takeaway
Shamir’s Secret Sharing is sneakily brilliant because it looks so simple. Polynomials? We learned those in high school. But that simplicity hides incredible power: a mathematically perfect way to split trust, with security properties that hold up against even quantum computers.
Sometimes the best algorithms aren’t the most complex ones. Sometimes they’re the ones that make you slap your forehead and think, “why didn’t I think of that?”
That’s the beauty of elegantly simple algorithms. They hide in plain sight, doing impossible-seeming things with elementary mathematics.
Next in the series: Bloom Filters - The data structure that’s okay with being wrong (sometimes)
Further Reading:
- Shamir’s original 1979 paper - Surprisingly readable
- Implementation considerations for production systems
- Example implementation: Secret Sharing Demo